Spying, honey pots, blackmail, extortion, and the basic values of Kosher Nostra from Altman to Ellison, so, just don’t look at the walking hemorrhoid Dershowitz as the only example!
Apr 17, 2026
Jews just don’t ask why Jews are so mean. Why they don’t look in the mirror. I mean, look, sort of like me looking in the mirror every time a teacher — K12 or higher ed — is accused of and found guilty of, well, messing around with students.

College teachers (professors, lecturers, TAs) dating students is generally discouraged or banned due to severe power imbalances and conflicts of interest. While rarely illegal if the student is over 18, it is heavily regulated, often requiring disclosure to HR to eliminate supervision, grading, or influence. Such relationships often violate university policy.

“What you should do is have a definitive policy one way or the other, where faculty and administrators decide which way is the best way to go — not start to carve out situations,” Miltenberg said. “What if it’s a dean with no direct academic role for the student, or a professor in a different department, or an adjunct? There are a lot of questions that will arise, with too many anomalies as far as circumstances.”
A sunset provision might work in the future, when colleges and universities “start to offer a fair, transparent and equitable process” to all parties in a Title IX case, Miltenberg said. Just not now. He recalled a case in which a faculty member taught only a core class, meaning there was no chance he would teach his students twice. But a relationship between the professor and one of his former students “didn’t go well,” Miltenberg said. “There was a complaint, and the faculty member lost his job.”
That’s what happened to John Barrett, an assistant professor of developmental studies at Bloomsburg University in Pennsylvania, in 2017. According to court documents, Barrett sent a student of his a Facebook friend request at the end of the spring 2015 semester, when she was in his class. The two corresponded over the summer about the student’s writing. Back on campus in the fall, the student asked to meet Barrett for coffee, and they began dating. Their sexual relationship lasted through the next summer.
The pair remained friendly for a time after breaking up, but the student eventually confronted Barrett about a relationship he was having with a second former student of his. The first student later filed a complaint with the university, alleging that Barrett had touched her genitals while she was sleeping during their relationship. The university investigated and terminated Barrett based on his poor professional judgment and the alleged touching without consent (which he denied, and which the student never brought up during their relationship).
Barrett filed a grievance with his faculty union, and an arbitrator ordered his reinstatement. Bloomsburg fought the decision, but a state appeals court upheld it last week. Bloomsburg doesn’t prohibit student-faculty relationships unless a supervisory relationship exists, and it no longer did in Barrett’s relationships, the court determined.
OF COURSE I think about my colleagues, my profession, when I read stories about that problem in colleges and even fucking k12!
Now now now, the Jewish religion does permit this shit: retribution, blackmail, bilking, raping, murdering, and starving. Oh, it’s just ‘those Jews’ in Israel?

In August of 2024, CCTV footage was leaked from Sde Teiman, Israel’s torture dungeon for detained Palestinians, showing the gang rape of a Palestinian prisoner by IDF militants.
10 of the IDF militants were arrested for the gang rape , and five were charged in February of last year for causing “broken ribs and a punctured lung” along with stabbing, “the detainee in the buttocks, causing rectal injury.”
Middle East Eye reported that , “Two suspects were found to have failed polygraph tests when asked whether they had inserted an object into the detainee’s anus or were concealing the identity of the person responsible. They denied both, but the examiner concluded they were being deceptive.”

Yoel Donchin, the doctor who examined the victim at Sde Teiman, said , “doctors found intestinal tears and broken ribs,” and that “We saw that he had a stab wound in the anus,” adding, “I saw how the soldiers there behave. I saw how they bring in the detainees and how they force them to sing songs. I saw a wounded person who had been abused and beaten severely.”
After the IDF rapists were questioned by Israeli military police, “right to rape rallies” took place outside of Sde Teiman, where members of the radicalized Israeli public demanded the IDF militants be freed.
In March of this year, the Israeli army dropped the charges against the five IDF militants , a move that was celebrated by Israel’s genocidal Defense Minister, Israel Katz, who said, “The role of the IDF’s legal system is to defend and protect soldiers who are bravely fighting monsters in war – not the rights of Nukhba terrorists”.
Now, the IDF has sanctioned the use of rape against Palestinians by allowing the five IDF militants to return to service.

This week, two lists were published which outed the biggest Zionist tools in US office: one for Republicans and one for Dems, because here in the US we have a bipartisan array of political suckage.
First the Dems: Bernie Sanders introduced a bill in the Senate that would block the sale of bombs to Israel. It failed, in part because of seven Democrats who betrayed their base to side with the AIPAC lobbyists who own them:
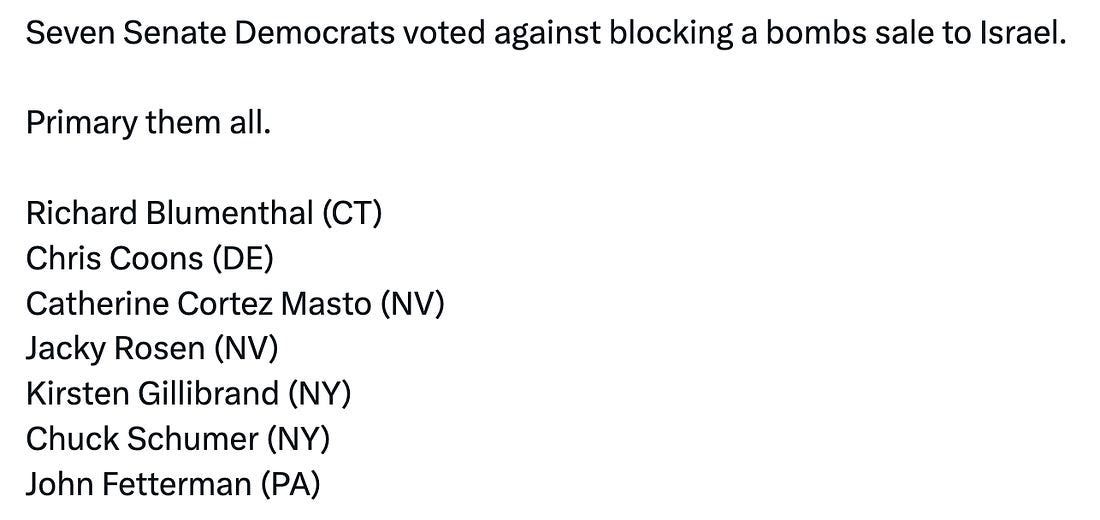
The list includes arch-Zionist / Senate minority leader Chuck Schumer, who, as the the plummeting of Israel’s reputation spreads to the Senate, has begun facing calls from his colleagues to resign in shame.
The second list shows, after years of being called a foreign agent in the pocket of Putin by corporate spokespeople at CNN and MSNBC, that Donald Trump really is a foreign agent. It’s just not the Russians who own him.
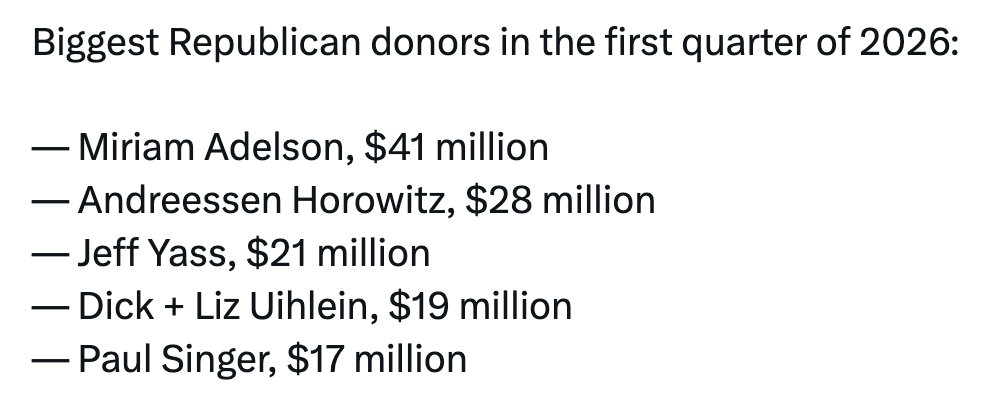
Of this list of Trump owners, 4 of 5 are Jewish, and all are radical Zionists. This is how Epstein-lawyer Alan Dershowitz has now begun blackmailing the president, saying that Israel will
“fight, even if it means confrontation with President Trump. We will take care of Trump. I met with him…and he was very receptive about Iran…and Miriam Adelson has met with him…”
Join Katie and Aaron for a deep dive into the Zionist lobby’s dealings with Trump and greedy Dems, plus Stephen Miller nearly slips up and calls for a “final solution” carried out by Israel, and Fox News’ Maria Bartiromo uses ChatGPT to get some questionable information.

“I have many jobs as leader… and one is to fight for aid to Israel – all the aid that Israel needs. I will continue to fight for it,” Chuck Schumer told a gathering of Jewish groups at the Park East Synagogue in New York in February.

There’s a piece out from Zeteo’s Asawin Suebsaeng, and the upshot is this: a significant number of senior Trump administration officials are genuinely worried they’re going to end up in prison.
Stephen Miller. Pete Hegseth. Officials spread across multiple departments. According to administration insiders, they’re watching the polling data, they know Democrats are likely to retake the House in 2026, and they’re under no illusions about what that could mean.
They’ve already noticed Democratic politicians making increasingly public calls for aggressive prosecutions of Trump officials. One Trump aide described the trend as, quote, “kind of worrisome.” Many of these officials don’t believe that even presidential pardons will be enough to protect them once the political winds shift.
The Wall Street Journal reported last week that Trump has promised to sign mass pardons for administration officials before leaving office. But apparently that promise isn’t as reassuring as it sounds. Last year, multiple Trump officials quietly purchased new legal insurance and professional liability coverage in anticipation of future investigations and subpoenas.
The reality is setting in. These people know what they’ve done. And they’re starting to realize that history has a long memory.

Aaron: Noam Chomsky’s wife responds to Epstein controversy
Yeah, Katie and Aaron never question their own rabbis, their own upbringing, their own Jewishness when confronted with the hell on earth Jews seem to be unleashing out of proportion to their global total population.
[Based on the 2025 Forbes billionaire data, approximately 276 to 300+ individuals on the list are identified as Jewish or have Jewish heritage, representing about 9.1% of the world’s 3,028 billionaires. The number varies based on definitions of Jewish identity.]

Israel’s economy is rocking! Lots of Jewish American billionaires, too at Oracle, Nvidia, Google, few others. Great time to be Jewish!!
Numbers and tribal loyalties COUNT:
- The number of Israeli billionaires on the Forbes list has grown rapidly, reaching 52 in early 2026, a 24% increase in combined wealth, with major representation in technology, shipping, and real estate.
- Global Presence: While representing less than 0.2% of the world population, Jewish individuals often make up roughly 20% of the Forbes 400 richest Americans
The initiative is being led by Jewish philanthropists, including Igor Tulchinsky, and is focused on strengthening the work of Chabad representatives on the ground. In Israel, support is going toward families, soldiers, evacuees, and those directly affected by recent events, while globally, additional efforts include sending hundreds of rabbinical students to assist communities in over 300 cities, to make sure Jewish communities everywhere have access to a full and meaningful Passover experience.




Enough of this blasphemy of neuroperversity?


This is a very personal review of recent regional tragedies from Lebanese journalist and mother of three Marwa Osman. She talks about her own personal loss during ‘Black Wednesday’ when the Zionists carried out 150 airstrikes across Lebanon in 10 minutes, massacring civilians even in areas where Hezbollah has no presence. We also delve into the much-maligned Iranian ceasefire and what it means for the region, short, mid, and long term.
Trump declared, “my favourite thing is to take the oil in Iran”. He – or the rational part of his regime – actually wants Iran as a client-state where the US dictates how and where the oil flows.
But this war isn’t just about control over oil. It’s about control over the future – a future that otherwise increasingly looks like one without oil or the US at its centre. It’s a war of transition.
Supremacy
Trump’s illegal war on Iran – one of five oil-rich countries attacked by the US in the past year and a half – forms part of a broader assault on the emerging transition economy, one that includes an assault on green policies and renewable energy investments.
Trump’s war on Iran and on the future

Data Data Data Control Control Control:

Item 8 on the agenda for Home Depot’s 2026 Annual Meeting of Shareholders — virtual only, 9 a.m. Eastern — is a shareholder proposal filed by Neil Fisher and Meryl Loonin. They are asking the company’s Board of Directors to produce a report assessing the risks to customers’ data privacy rights that result from Home Depot sharing sensitive data with third parties. The data in question includes gender, race, ethnicity, and geolocation.
The vehicle is Flock Safety’s Automated License Plate Reader cameras — ALPRs, in the business — deployed across Home Depot locations nationwide. According to the proponents’ filing, Flock’s network is accessible to federal law enforcement. The proposal cites what it calls “frequent immigration enforcement raids occurring near its stores” as a source of reputational risk.
That is a careful, lawyerly way of saying something plainly: if ICE wants to know who drove to Home Depot, the infrastructure may already exist to tell them.
The Board of Directors recommends shareholders vote against the proposal. Its position is that existing safeguards and internal risk management programs are sufficient to handle the concern.
That answer will not satisfy everyone who shops at Home Depot.
The company’s customer base includes millions of immigrants — documented and undocumented alike — who buy lumber, pipe fittings, and paint to build and maintain the homes of this country. Those customers have no way of knowing, when they pull off the highway and into the lot, that a networked camera is recording their presence and linking it to a plate that can be queried by federal agents.
The proposal requires a vote because it is considered a non-routine matter under exchange rules. That means banks and brokers holding shares in street name cannot cast a vote on their clients’ behalf without explicit instructions. Shareholders of record as of March 23, are eligible to vote.
Home Depot is not alone in facing this kind of scrutiny. Across corporate America, the question of what data companies collect, who can access it, and under what legal authority is colliding with an immigration enforcement environment that has grown more aggressive by the week. The difference here is that the mechanism — a private surveillance vendor with federal reach embedded in a retail parking lot — has a name: Flock Safety.


Jewish fucking values, dude, Aaron, Katie, Max, et al, Finkelstein:
Larry Ellison, the co-founder of Oracle, advocates for unifying national and personal data primarily to maximize the efficiency of Artificial Intelligence (AI) and enhance societal security. He argues that current data is too “fragmented” across thousands of separate databases, preventing AI from solving complex problems effectively.

His stated reasons for this massive data consolidation include:
- Optimizing AI Performance: Ellison believes AI models can only reach their full potential if they are fed unified national datasets rather than isolated silos of information.
- Improving Public Services: He claims a central database could transform healthcare by unifying medical records and DNA data to find earlier treatments, as well as improve agriculture and infrastructure.
- Preventing Fraud: By using AI to analyze government spending data in one place, he suggests countries could identify “vast amounts of fraud” and waste more effectively.
- Enforcing “Best Behavior”: Controversially, Ellison supports 24/7 AI-powered surveillance of both citizens and law enforcement. He suggests that if everyone is constantly being recorded and reported, they will maintain their “best behavior”.
- Security and National Defense: He has long maintained that such data collection is “essential” for national security, specifically for identifying and preventing threats like terrorism.

How many fucking apps does the average worker have to have on his or her fucking surveillance phone?
Common Types of Work-Related Apps
- Communication & Training: Instant messaging and video training modules (e.g., MindForge, Workday).
- Workflow Management: Apps for shift scheduling, time tracking, and digital project plans (e.g., Raken, Procore).
- Security & IT: Mobile Device Management (MDM) software that creates a secure “work profile” to separate company data from personal files.
- EHS (Environment, Health, and Safety): Safety checklists and incident reporting tools used to build a “culture of safety” on jobsites
What the Law Actually Says
No federal statute prohibits employers from requiring employees to use personal devices for work purposes. Under at-will employment (the standard in all U.S. states except Montana), employers can set conditions of employment including the tools and technology employees must use to do their jobs.
[11 Reasons an employee app is a must-have for your workforce ]

Create a moral panic. Blame it on certain people. Commence monitoring. Deploy droves of security agents. Detain or remove the targets. Sound familiar?
My other fucking hat, a masters in urban and regional planning! Social control through planning and architecture!
Angel, Schlomo (1968). Discouraging Crime through City Planning (working paper no. 68). Berkeley: UC Berkeley Institute of Urban & Regional Development.
One of the earliest works published on crime prevention through urban design, this Jane Jacobs-inspired paper sketches out public space designs that enable mutual surveillance based on increased user density. Angel hypothesized that crime in public space emerged in a “critical intensity zone” between extremely low and high usage. To counter this victimization period, he proposed creating “evening squares” in which an optimally dense user population would prevent crime by mutually monitoring each other’s activities.
Bentham, Jeremy (2005). The Panopticon, or Inspection-House. Available online: http://cartome.org/panopticon2.htm/.
This abridged version of Bentham’s design and management plans for the panopticon prison provided the foundations for Foucault’s pioneering analysis of disciplinary spaces.
Blakely, Edward J. and M. G. Snyder (Spring 1998). “Forting Up: Gated Communities in the United States,” Journal of Architectural and Planning Research vol.15, no.1: 61–72.
Adapted from the authors’ influential book on the same topic, this article examines gated community residents’ desire for social status and exclusivity. The authors argue that the gating reflex is on the rise across the social spectrum, and is no longer a status symbol and defensive feature reserved for the elite.
Borden, Iain (November/December 1996). “Thick Edge: Architectural Boundaries and Spatial Flows,” Architectural Design vol. 66: 84–7.
In this brief but imaginative essay, the author explores the postmodern city’s use of borders and edges as ways to control spatial circulation and social interaction. These boundaries are envisaged as extensions of capitalism’s power to direct spatial and social relations towards consumption.
Boyne, Roy (May 2000). “Post-Panopticon,” Economy and Society vol. 29, no. 2: 285–307.
The author reconsiders the concept of panopticism in the wake of increasing surveillance of public and private life. The author reviews arguments that the panopticon model of centralized surveillance is outdated in a world dominated by the decentralization of knowledge. Acknowledging that the diagram of surveillance has changed, he concludes that new forms of surveillance still adhere to a panoptical impulse.
Bring, Mitchell (May 1978). “TV Surveillance: the Not-So-Hidden Dimension of Public Space,” Landscape Architecture vol. 68: 189–90, 231–2.
This early article discusses what was, at that time, an emerging trend of using closed circuit television surveillance in public space design. The author warned that video surveillance threatens democratic use of public space.
Carter, Michael (1995). “Guerilla Programming of Video Surveillance Equipment.” Available online: http://www.notbored.org/gpvse.html.
Originally published as a pamphlet manifesto, this concise article calls for staging guerilla performances in front of surveillance cameras as acts of resistance. The article is considered a founding document for the growing performance-based surveillance resistance movement.
Crowe, Timothy (1991). Crime Prevention through Environmental Design: Applications of Architectural Design and Space Management Concepts. Boston: Butterworth-Heinemann.
One of the most often-cited sources on Crime Prevention Through Environmental Design, the manual outlines CPTED’s origins, principles, and applications. Written in textbook like prose and complete with several diagrams, maps, and appendices, the book is a helpful desk reference for CPTED-minded planners.
Cuff, Dana (September 2003). “Immanent Domain: Pervasive Computing in the Public Realm,” Journal of Architectural Education vol. 57, no. 1: 43–49.
The author examines how expanding and networked computer technologies are changing the way people experience public space. The author’s take on pervasive computing posits a “double view, utopian and dystopian.” On one hand, pervasive computing facilitates expanded communication and technological innovation; on the other, it increases surveillance capabilities and hastens the loss of privacy. Cuff contends that the future of the public realm is inevitably intertwined with the growth of pervasive computing.
Davis, Mike (2003). “Scanscape,” Quaderns vol. 237: 52–57.
In this brief essay, the author describes how increasing surveillance technologies and the LAPD’s expansion into city planning decision-making have turned downtown LA into a “scanscape,” a heavily surveilled space in which white-collar office workers and tourists are made to feel safe.
Davis, Mike (1992). City of Quartz: Excavating the Future of Los Angeles. New York: Vintage.
In this groundbreaking exposé of a dystopic postmodern Los Angeles, Davis describes and critiques elements of the built environment that make up what he calls “Security-Obsessed Urbanism”: gated properties, surveillance cameras, ‘bum-proof’ benches, panopticon-inspired architecture, privatized security services and militarized police forces.
DeLanda, Manuel (2001). “Panspectron,” in Joy Garnett, Rocket Science, exhibition catalogue, 12.04.01–19.05.01, ISBN 1929032072. Available online: http://www.firstpulseprojects.com/panspectron.html/.
In this brief essay, the author reviews a range of military surveillance technologies, including satellites, spy planes, x-rays, radio waves, infrared systems, multispectral scanning, and night vision systems. Citing their increasing use on civilians and in cities, DeLanda posits that we are transitioning from a panopticon to a wider panspectron model.
DeLanda, Manuel (1986). “Policing the Spectrum,” in Michel Feher & Sanford Kwinter (eds), Zone 1/2: City, New York: Urzone/Johns Hopkins University Press: 177–87.
DeLanda reviews the US military surveillance system’s attempt to police abstract spaces. His review covers crypotology, the covert mapping of Tibet, NSA and CIA surveillance operations, early forms of computer hacking, cellular automata, and the abstraction/extraction of bodily knowledge for the purposes of discipline and control. He envisions a resistance movement in which theorists expand their analyses to identify ways out of this surveillance system.
De Lint, Willem (2000). “Arresting the Eye: Surveillance, Social Control and Resistance,” Space and Culture vol. 9, no. 9: 21–49.
The author opens up the discourse on surveillance by suggesting surveillance technologies are not merely instruments of social control. The article highlights benevolent uses of surveillance technologies that enable governments to understand the needs of a population. Ultimately, De Lint contends that surveillance and social control are not synonymous.
Ellin, Nan (ed) (1997). Architecture of Fear. New York: Princeton Architectural Press.
The comprehensive volume includes twenty essays that examine how fear, insecurity, and social anxiety shape contemporary urban space. The Security City, rife with surveillance systems, gated communities, privatized public spaces, defensible houses, etc., developed in response to these fears, and ironically perpetuates insecurity. The authors represent a cross-section of perspectives making for a well-balanced analysis that is, on balance, rooted in architectural criticism.
Fabijancic, Tony (September 2001). “The Prison in the Arcade: A Carceral Diagram of Consumer Space,” Mosaic vol. 34, no. 2: 141–157.
The author synthesizes the writings of Foucault and Walter Benjamin in this examination of the emergence of a carceral diagram in 19th century shopping arcades. The author situates this development in an era of disciplinary transformation that saw Haussmann’s restructuring of boulevards and the birth of crowd psychology.
Farrar, Margaret E. (Fall 2000). “Health and Beauty in the Body Politic: Subjectivity and Urban Space,” Polity vol. 33, no. 1: 1–23.
The author, a political scientist, synthesizes the work of Foucault, Lefebvre, and Kristeva to explain how power and spatial subjectivity informed early 20th century American open space and housing reform policies. The author argues that such spatial planning practices enabled power to be manifested in cities and in the citizenry. The article represents a rare instance in which a political scientist successfully deals with the topic of space, power, and city planning.
Finn, Mary A. and S. Muirhead-Steves (June 2002). “The Effectiveness of Electronic Monitoring with Violent Male Parolees,” Justice Quarterly vol. 19, no.2: 293–312.
The authors assert that electronic monitoring of violent male offenders is an effective deterrent to recidivism. They base their position on a study that showed electronic monitoring reduced return to prison rates and parolee substance abuse rates. The authors maintain that expanded electronic monitoring of high risk offenders should be explored.
Flusty, Steven (September 2001). “The Banality of Interdiction: Surveillance, Control and the Displacement of Diversity,” International Journal of Urban and Regional Research vol. 25, no. 3: 658–664.
In this follow-up to his book Building Paranoia, Flusty describes how surveillance, strict codes of conduct, and enclavism have become normalized in Los Angeles. Consequently, says Flusty, the critical literature has diminished and increasing social control seems to be an acceptable, routine function of social and spatial relations.
Flusty, Steven (April 2000). “Thrashing Downtown: Play as Resistance to the Spatial and Representational Regulation of Los Angeles,” Cities vol. 17, no. 2: 149–58.
The article describes the privatization and corporatization of downtown public space and forms of resistance centered on “play.” Recounting his walking tour of downtown LA’s Bunker Hill, Flusty identifies the playful acts of resistance he observed: skateboarding, public poetry reading, and performative “bubble-blowing.”
Flusty, Steven (1994). Building Paranoia: The Proliferation of Interdictory Space and the Erosion of Spatial Justice. West Hollywood, CA: Los Angeles Forum for Architecture and Urban Design.
The author categorizes various spatial and architectural typologies that convey insecurity in the built environment, including varying examples of interdictory spaces and models of “paranoid architecture.” Unlike other writers on the critical left, Flusty’s descriptive analysis is less inflammatory, as he is more concerned with situating these typologies in broader public discourse.
Foucault, Michel (1975). Discipline and Punish: The Birth of the Prison. New York: Vintage.
In this pioneering study, Foucault traces modern society’s development into a panopticon-like dystopia characterized by diffuse and pervasive surveillance and spatial control practices. Virtually all criticism of surveillance-centered dystopias stem from Foucault’s lyrical critique of disciplinary urban spaces.
Haggerty, Kevin D. and R. V. Ericson (December 2000). “The Surveillant Assemblage,” British Journal of Sociology vol. 51, no. 4: 605–622.
In this excellent essay, the authors augment the dominant Foucauldian-Orwellian discourse on surveillance society with an analysis of expanding and abstracted systems of surveillance. Citing Deleuze and Guattari’s theory of rhizomatic flows, the authors contend that technological surveillance has become a “surveillant assemblage” of decentralized gazes in real and virtual space.
Heavy Trash (2005). “(internet website).” Available online:
http://heavytrash.blogspot.com/
This website is the virtual headquarters for an anonymous group of architects, artists, and planners who erect large, disposable art objects around fortified city spaces in order to call attention to these exclusive areas. Their resistance art has included a bridge spanning a gate at a public park and viewing platforms erected outside several gated communities.
Howeler, Eric (2002). “Anxious Architectures: The Aesthetics of Surveillance,” Archis no. 3: 9–18, 20–3.
The author describes the assortment of security technologies being incorporated into architectural design, including CPTED and defensible space techniques, remote alarm and surveillance systems, and global positioning devices.
Incirlioglu, Emine O. and Z. Tandogan. (April 1999). “Cultural Diversity, Public Space, Aesthetics and Power,” European Journal of Intercultural Studies vol. 10, no. 1: 51–61.
The authors argue that inclusion and exclusion in public space can be studied through aesthetic criteria. Put bluntly: aesthetically pleasing, civilized and desirable persons are allowed in public spaces; aesthetically undesirable persons, such as the homeless or certain “visible foreigners”, are excluded. The use of such an aesthetic criteria precludes the democratic use of public spaces and mutual coexistence.
Jacobs, Jane (1961). The Death and Life of Great American Cities. New York: Vintage.
This groundbreaking opus vilifies modernist city planning for killing pedestrian life at the street level. In response, Jacobs calls for a return to dense, diversified urban environments reminiscent of 19th century cities, where additional “eyes on the street” permit informal surveillance of public space.
Jeffrey, C. Ray (1971). Crime Prevention Through Environmental Design. Beverly Hills, CA: Sage Publications.
The book title is somewhat misleading since Jeffrey devotes only one chapter to crime prevention through environmental design in which he talks little about physical security elements and more about socio-psychological factors relating to crime prevention. Nevertheless, in this book Jeffrey coins the term CPTED and establishes the ideological basis for design-based crime prevention which gives rise to the dystopian security city.
Jencks, Charles (March/April 1995). “Aphorisms on Power?” Architectural Design vol. 65: 20–3.
This brief essay by the noted architectural theorist and historian explores architects’ ability to wield positive creative power and negative coercive power. Although coercive power enables a stronger degree of spatial control, it is paradoxically more fragile. Consequently, the author says, coercive power gives way to creative power.
Jones, Peter (1999). “Building the Empire of the Gaze: The Modern Movement and the Surveillance Society,” Architectural Theory Review vol. 4, no. 2: 1–14.
Retracing the trajectory of the modern movement starting from its origins in ocularcentrism, Jones illustrates how modernist architecture’s salient features — glass, the interior, the house, and the factory — contributed to the rise of what Foucault called surveillance society. Jones’ critique is effective but could benefit from more in-depth analysis, including additional evidence and elaboration.
Katyal, Neal K. (March 2002). “Architecture as Crime Control,” 111 Yale Law Journal no. 1039.
This law review article is extraordinary in that it focuses little on law and instead outlines crime prevention through environmental design and its sociopolitical implications for the built environment. Written primarily for law professionals with limited knowledge of the topic, Katyal’s article is thorough, comprehensive, and filled with painstaking detail characteristic of law reviews.
Kawash, Samira (Winter 1998). “The Homeless Body,” Public Culture vol. 10, no. 2: 319–339.
The author analyses the construction of the homeless body as a public discourse and a deviant counterpart to the abstract public body. The placelessness and uncertainty of the homeless body is compared to the fixity and certainty of the public spaces they inhabit. The author catalogs strategies to control the homeless’s use of public space which result in the exclusion of homeless bodies.
Koskela, Hille (2000). “The Gaze Without Eyes: Video Surveillance and the Changing Nature of Urban Space,” Progress in Human Geography vol. 24, no. 2: 243–265.
The article refutes the argument that urban space has become oppressive, dystopic and prison-like through the proliferation of video surveillance cameras. Although Koskela agrees that a surveillance camera’s “gaze” represents a form of invisible power and that cameras create asymmetries of power in space, she ultimately concludes that cities, which are publicly accessible, democratic spaces, cannot reasonably be compared to prisons.
Leman-Langlois, Stéphane (2002). “The Myopic Panopticon: The Social Consequences of Policing through the Lens,” Policing and Society vol. 13, no. 1: 43–58.
The author argues that the police’s reliance on video surveillance technologies is ineffective and inadvisable because surveillance cameras have a “myopic” purview. Monitoring surveilled spaces channels police attention into fixed spatial parameters. Policing, says the author, becomes a reactive activity dependent on observing crimes in progress.
Leong, Sze Tsung (1998). “Readings of the Attenuated Landscape,” in Bell, M. and S. T. Leong. (eds) Slow Space. New York: Monacelli Press.
The author uses Foucault’s tripartite of sovereign power, disciplinary power, and bio-power as well his concept of heterotopia to explain the contours of America’s “attenuated landscape,” that is, postindustrial cityscapes characterized by disorientation and absence. Leong effectively employs Detroit and Houston as models of attenuation.
Levin, Thomas Y. et al. (2002). Ctrl [space]: Rhetorics of Surveillance from Bentham to Big Brother. Karlsruhe, Germany: ZKM Center for Art and Media; Cambridge, MA: MIT Press.
The anthology is a collection of scholarly essays, interview transcripts, images, and performance art synopses relating to technology and surveillance. The individual works are informative, humorous, creative, and provocative, and provide evocative counterpoints to arguments favoring increased public surveillance. This critical anthology can be read as a catalog of resistance efforts against surveillance.
Litz, Stefan A. (2000). “The Fortified Society: Social Exclusion as a Result of Privatization and Fortification of Space,” Berlin Journal of Sociology vol. 10, no. 4: 535–554.
Focusing on the US, the author discusses the causes, typologies, and implications of exclusionary and fortified urban space. The article includes a thorough discussion of elements of the built environment that enable exclusivity: walls, gated entries, surveillance systems, privatized public spaces, and private police forces. The author contends that, in an advanced capitalist society like the US, the purpose of architectural fortification and social exclusion is to distance oneself from “undesirable persons and social groups.”
Lynch, Mona (October 2001). “From the Punitive City to the Gated Community: Security and Segregation across the Social and Penal Landscape,” University of Miami Law Review vol. 56, no. 1: 89–111.
The law review article examines how society has taken on the characteristics of prisons. The author compares the partitioned-off spaces of gated communities to prisons, attributing this synthesis to cultural, political, economic and structural changes and psychological anxieties in the Security City.
Markus, Thomas A. (March/April 1995). “What Do Buildings Have to Do With Power?” Architectural Design vol. 65: 8–19.
The writer examines how power manifests in buildings. His analysis begins with a discussion of language as a system of explaining and understanding form. He says buildings are constructed using formal architectural languages that communicate operative power constructs such as structure, control, and surveillance.
Nellis, Mike (May 2005). “Out of this World: The Advent of the Satellite Tracking of Offenders in England and Wales,” Howard Journal of Criminal Justice vol. 44, no. 2: 125–150.
This recently published article examines emerging satellite tracking and electronic monitoring technologies in the United Kingdom. The author praises satellite tracking for enabling police authorities to monitor individual offenders’ movements and contends that electronic monitoring will open up avenues to more humanistic approaches to offender supervision.
Newman, Oscar (1973). Architectural Design for Crime Prevention. Washington: National Institute of Law Enforcement and Criminal Justice.
One of the earliest comprehensive studies on design-based crime prevention, the book outlines Newman’s theory of Defensible Space and describes its application in cities. Defensible Space entails four basic tenets: Territoriality increases residents’ control of public space, Natural Surveillance enables visibility, Strategic Juxtapositions create safe zones, and distinctive Building Images create a sense of spatial and architectural order.
Newman, Oscar (1975). Design Guidelines for Creating Defensible Space. Washington: National Institute of Law Enforcement and Criminal Justice, Law Enforcement Assistance Administration, U.S. Department of Justice.
The book updates Newman’s theory, incorporating socioeconomic and demographic factors absent from his original work. Using less hyperbole, Newman provides several Defensible Space design guidelines for architects, planners, and policy makers. A cynical reading might infer that this work is a “how-to” guide for creating legitimated dystopian security cities.
Nieto, Marcus (June 1997). “Public Video Surveillance: Is it an Effective Crime Prevention Tool,” California Research Bureau, CRB-97–005. Available online: http://www.library.ca.gov/CRB/97/05/index.html/.
This extensive government report assesses the effectiveness of video surveillance as a crime deterrence method and reviews legal and constitutional issues relating to surveillance of public spaces.
Nisbet, Nancy (2004). “Resisting Surveillance: Identity and Implantable Microchips,” Leonardo vol. 37, no. 3: 210–16.
The art review essay explains artist Nancy Nisbet’s installations commenting on surveillance through bodily microchip implantation and recounts how surveillance technologies are influencing identity and subjectivity.
Outtes, Joel (April 2003). “Disciplining Society through the City: The Genesis of City Planning in Brazil and Argentina (1894–1945),” Bulletin of Latin American Research vol. 22, no. 2: 137–164.
The author traces the evolution of city planning in Argentina and Brazil between the years 1894 and 1945. Employing a Foucauldian lens, Outtes interprets planning as a mechanism through which the state achieves spatial and social discipline from the production of orderly and hygienic cityscapes and the promotion of industrial culture. The author also examines how the pursuit of racist eugenics in Brazil ultimately “poisoned the planner’s discourse.”
Reynolds, Bryan and J. Fitzpatrick (Fall 1999). “The Transversality of Michel de Certeau: Foucault’s Panoptic and the Cartographic Impulse,” Diacritics vol. 29, no. 3: 63–80.
The authors synthesize Foucault’s theory of panopticism and de Certeau’s writings on everyday spatial practices to produce a complex and often times confusing framework for challenging spatialized power and subjectivity by undertaking transversal movements across cityspace. In short, transversality is the ability to cut across different spaces, disrupting existing power structures within them.
Rosenberg, Richard S. (1999). “The Workplace on the Verge of the 21st century,” Journal of Business Ethics vol. 22, no. 1: 3–14.
The article discusses how internet tracking, e-mail monitoring, background checks, drug screening, and video surveillance are bringing the Security City into the private realm of the workplace.
Schmidt, Annesley K. (1998). “Electronic Monitoring: What Does the Literature Tell Us?” Federal Probation vol. 62, no. 2: 10–19.
The literature review assesses several corrections programs using electronic devices to monitor the whereabouts and movements of offenders participating in home-based incarceration.
Schneider, Richard and T. Kitchen (2002). Planning for Crime Prevention: A Transatlantic Perspective. London; New York: Routledge.
This comprehensive study reviews design-based crime prevention strategies in the US and the UK. The authors outline the history of defensible urban design, provide thorough reviews of design-based crime prevention methods, and offer several recommendations to advance the general field of planning for crime prevention. Most noteworthy, the authors criticize the general neglect of crime as a planning issue and challenge city planners to take on more active roles in crime prevention.
Sipes, James L. (September 2002). “A New Kind of Scrutiny,” Landscape Architecture vol. 92, no. 9: 58–63.
The article reviews design-based technologies landscape architects are using to achieve spatial control in the Security City. These measures include: traffic bollards and circulation barriers, surveillance cameras, and biometric scanning devices such as facial recognition systems, hand readers, retinal scanners, and voice recognition systems.
Sniffen, Michael (7 July 2003). “US Develops Urban Surveillance System,” Akron Beacon Journal.
The newspaper article explains the Pentagon’s plans to create an urban surveillance system comprised of a network of cameras and satellites that will allow military authorities to monitor activities in non-US cities. The surveillance system will be capable of reading license plates and identifying individual faces in cities. Although the program is being developed for war zones, the author notes that the technology can be modified for homeland use.
Soja, Edward W. (2000). Postmetropolis: Critical Studies of Cities and Regions. Oxford; Malden, MA: Blackwell.
The book’s chapter on the Carceral Archipelago synthesizes several critical perspectives on what Soja describes as the “incarceration of cityspace.” Soja argues that globalization and economic restructuring have produced significant sociopolitical and economic imbalances that have created volatility in the contemporary metropolis. According to Soja, this volatility produced the need for security-obsessed urbanism as a means to keep the city from collapsing into chaos.
Sorkin, Michael (March 2003). “Can Architects and Planners use Security Concerns to Create more Humane Cities?” Architectural Record vol. 191, no. 3: 73–4, 76.
The author contends that security-centered urbanism devalues the notion of “the good city” and engenders urban anxiety, paranoia, and a fortress mentality. In the post-9/11 era and with violent crime primarily manifesting in cities, this fear is not completely unwarranted. The author proposes an approach to urban design that tries to balance the need for secure and comfortable spaces.
Surveillance Camera Players (November 1999). “Time in the Shadows of Anonymity: Against Surveillance, Transparency and Global Capitalism.” Available online: https://www.notbored.org/the-scp.html.
This position paper authored by a performance-based surveillance resistance movement advances a theory of surveillance predicated on increasing transparency in political, economic, and social relations. Their take on transparency as a political construct augments the literature on architectural transparency as a surveillant quality.
Whitely, Nigel (May 2003). “Intensity of Scrutiny and a Good Eyeful: Architecture and Transparency,” Journal of Architectural Education vol. 56, no. 4: 8–16.
The article traces the meaning of transparency in modernist architecture. Transparency has been alternately conceived as an emblem of open democracy, a symbol of technological progress, and a motif of capitalist urbanism. In the security centered 21st century, transparency in society and architecture is enabling pervasive surveillance.

